PHOTO
- The activity likely targets consumer users who do not have the benefits of enterprise-grade security on their home computers.
Dubai, United Arab Emirates: Threat actors often target home users because they do not have the same resources or knowledge to defend themselves from attackers compared to enterprises. While the financial gain might not be as large as attacks perpetrated on corporations, the individual victims likely still have data like credit cards, cryptocurrency wallets, and other personal identifiable information (PII) stored on their computers which can be lucrative to criminals.
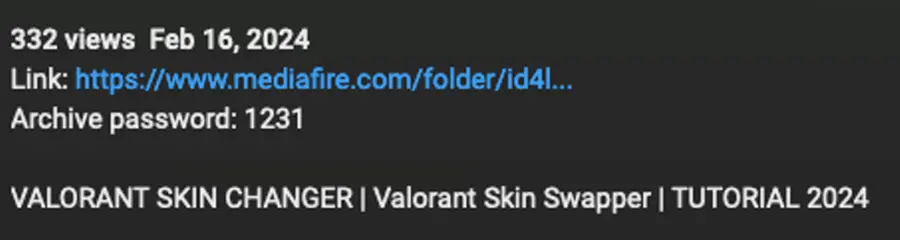
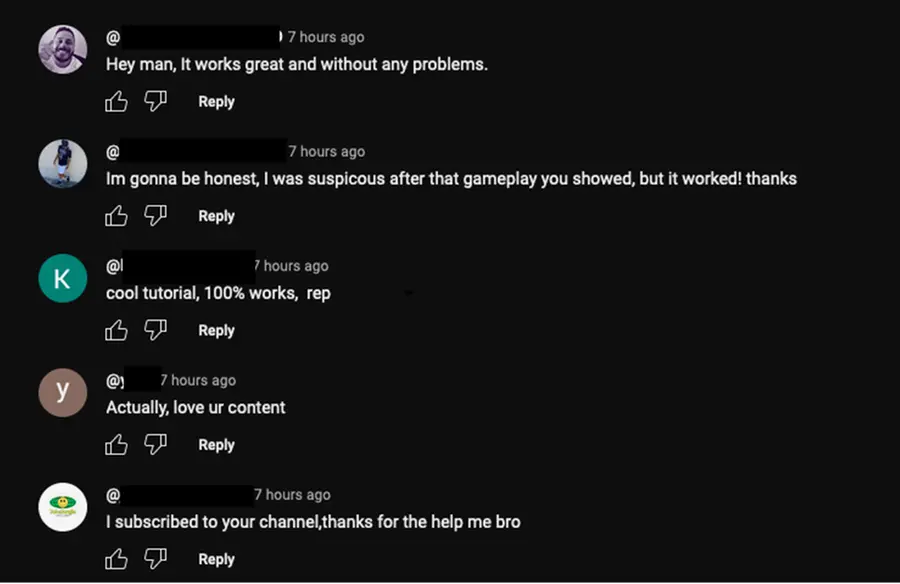
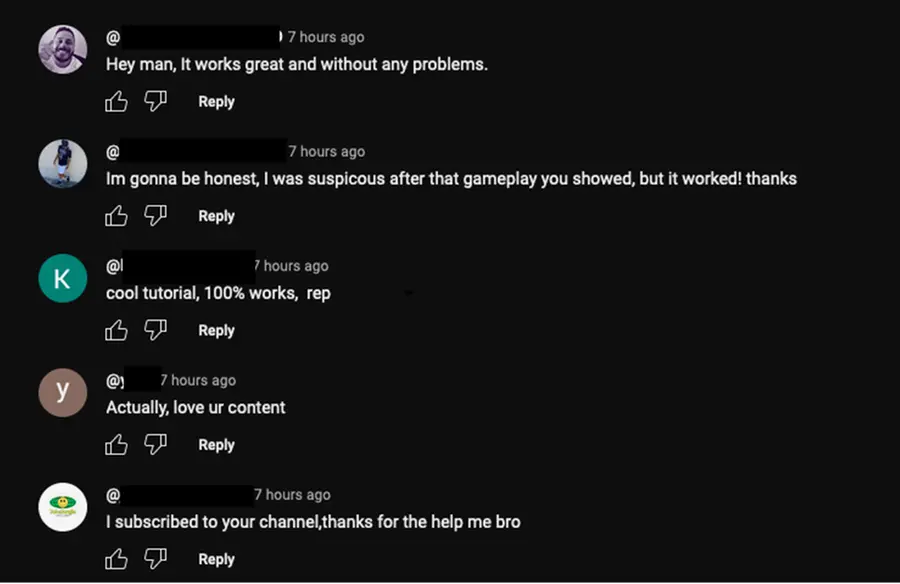
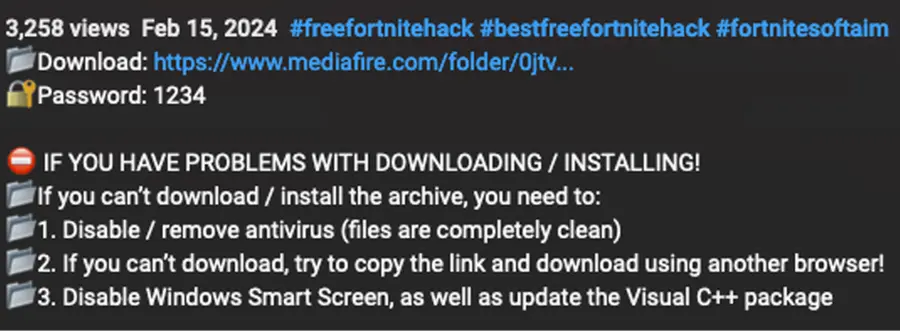
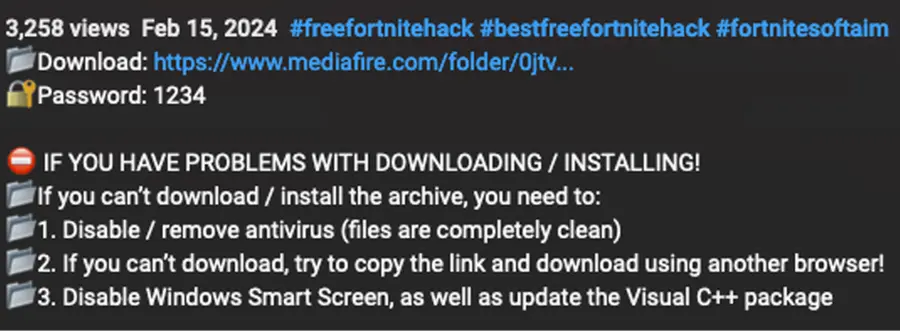
Proofpoint Emerging Threats has observed information stealer malware, including Vidar, StealC, and Lumma Stealer, being delivered via YouTube in the guise of pirated software and video game cracks. The videos purport to show an end user how to do things like download software or upgrade video games for free, but the link in the video descriptions leads to malware. Many of the accounts that are hosting malicious videos appear to be compromised or otherwise acquired from legitimate users, but researchers have also observed likely actor-created and controlled accounts that are active for only a few hours, created exclusively to deliver malware. Third-party researchers have previously published details on fake cracked software videos used to deliver malware.
The distribution method is particularly notable due to the type of video games the threat actors appear to promote. Many of them appear to be targeted at younger users, including games popular with children, a group that is less likely to be able to identify malicious content and risky online behaviors.
Proofpoint Emerging Threats reported over two dozen accounts and videos distributing malware to YouTube, which removed the content.
Example Account
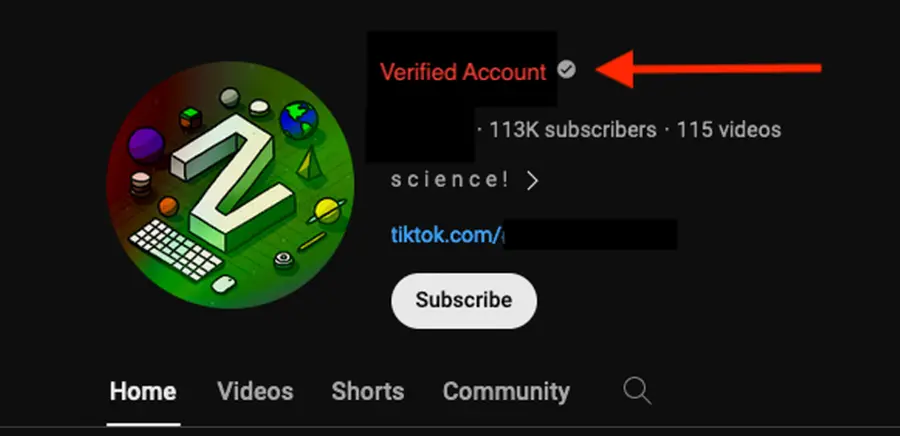
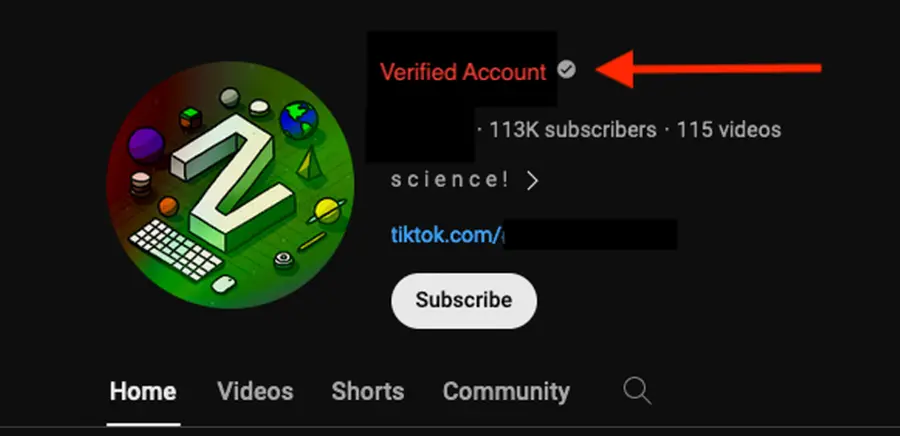
Suspected compromised accounts (or potentially sold to a new “content creator”) are used to deliver malware. Indicators of a suspected compromised or otherwise acquired account include significant gaps of time between the videos posted, content that vastly differs from previously published videos, differences in languages, and descriptions of the videos containing likely malicious links, among other indicators.
One of the accounts has around 113,000 subscribers, and it displays a grey check mark that indicates the account owner has met verified channel requirements, including verifying their identity.
When Proofpoint researchers identified the account, the majority of the account’s videos had been posted one year or more previously, and all had titles written in Thai. However, when the account was identified, twelve (12) new English language videos had been posted within a 24-hour period, all related to popular video games and software cracks. All of the new video descriptions included links to malicious content. Some of the videos had over 1,000 views, possibly artificially increased by bots to make the videos seem more legitimate.
Empress Impersonation
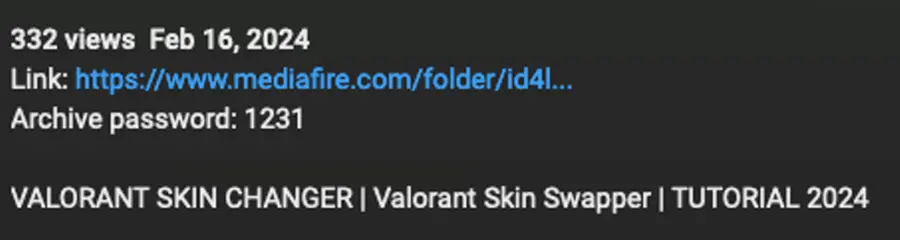
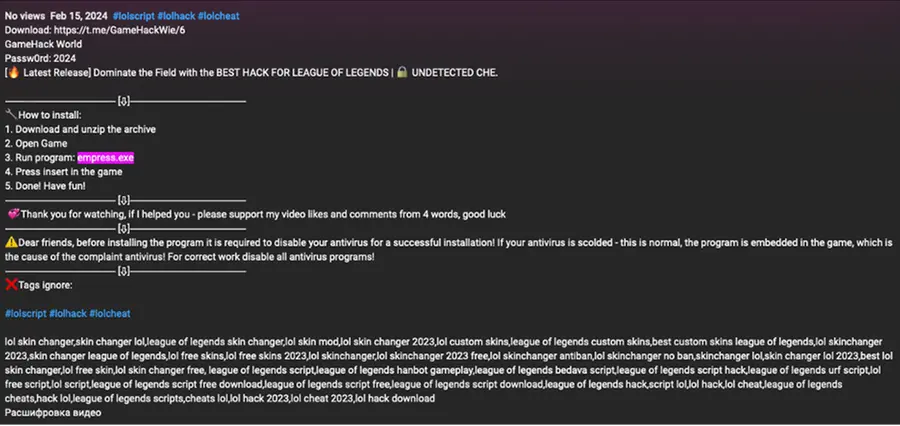
Proofpoint identified multiple videos purporting to distribute Empress video game cracks. Empress is a well-known entity in the software piracy community. In one example, a user purported to distribute cracked “League of Legends” content on the video-sharing platform. The video description contained a Telegram URL that led to a post containing instructions on how to download the content and a MediaFire URL leading to a RAR archive containing an executable. The file was named “empress.exe” to appear to come from the popular software piracy resource and appear to be “legitimate.”
Discord Server Distribution
Another payload distribution method via YouTube video descriptions that differs from MediaFire URLs is Discord URLs. Proofpoint observed threat actors creating and managing a Discord server that has different malware for each game. The Discord link in the video description will direct users to a Discord channel that hosts the files available for download and includes instructions on how to download and install them.
Proofpoint observed multiple distinct activity clusters distributing information stealers via YouTube and does not attribute the activity to a tracked threat actor or group. The techniques used are similar, however, including the use of video descriptions to host URLs leading to malicious payloads and providing instructions on disabling antivirus, and using similar file sizes with bloating to attempt to bypass detections. Based on the similarities of the video content, payload delivery, and deception methods, Proofpoint assesses that the actors are consistently targeting non-enterprise users.
Proofpoint does not currently have visibility on how the identified YouTube accounts may have been compromised and YouTube has been quick to remove accounts reported by the Proofpoint Research team.
End users should be aware of the techniques used by threat actors to entice users into engaging with video game content purported to help them cheat or bypass paid functionality.
Media Contact:
Sara Seggari
sara.seggari@bpggroup.com