Research based on the analysis of incidents reported to customers of Kaspersky Managed Detection and Response (MDR) has revealed that Security Operations Center (SOC) analysts discovered more than three high-severity incidents with direct human involvement every day in 2022.
The efficiency that external specialists provided while dealing with cybersecurity solutions and requirements of special knowledge were the main reasons for the companies to outsource external experts in 2022. To address the lack of gaps in expertise among IT Security professionals and provide them with insights on the current threat landscape, Kaspersky analyzed anonymized customer incidents detected by its MDR service.
Kaspersky’s annual Managed Detection and Response Analyst Report[1] showed the high-severity incidents required an average 43.8 minutes to be detected by Kaspersky MDR[2]. Due to an increase in human-driven attacks this processing time grew by approximately 6% compared to previous year, as they take up more of SOC analyst time.
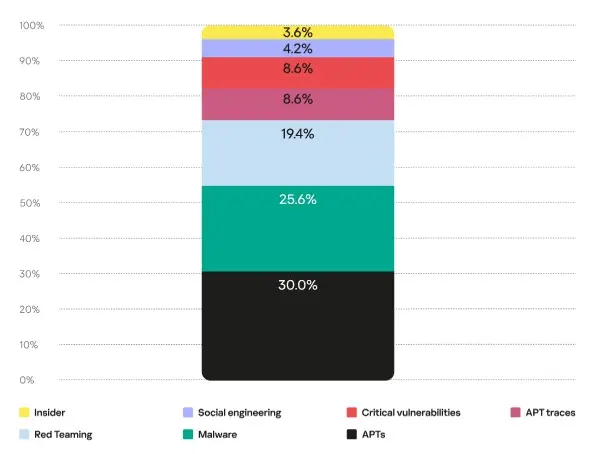
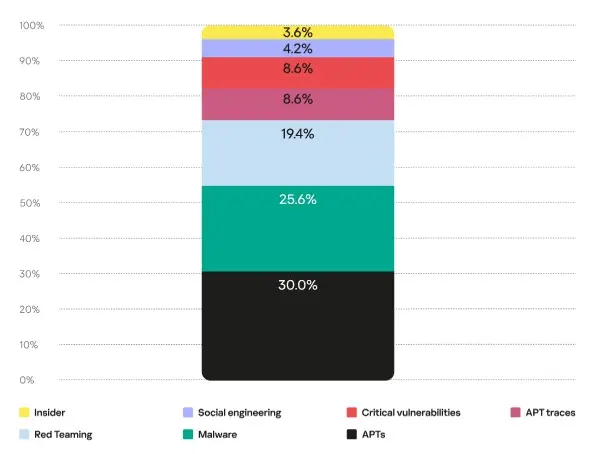
Regarding the nature of such incidents, 30% of them were associated with APTs[3], 26% accounted for malware attacks, and just over 19% resulted from “ethical hacking” (pentests, red teaming or any other types of cyber exercises conducted in customers’ infrastructures either for the security assessment of IT systems or to test the operational readiness of the MDR service). The proportion of incidents involving publicly available critical vulnerabilities and the detection of traces of previous attacks involving humans was around 9%. The remaining incidents resulted from the successful use of social engineering techniques or were linked to insider threats.
‘The MDR report shows that sophisticated attacks driven by humans continue to grow. They require more resources to be investigated and they take up more of SOC analyst time as this type of attack lends itself to automation to a lesser degree. To detect these attacks efficiently we recommend companies to implement comprehensive threat hunting practices combined with classic alert monitoring,’ comments Sergey Soldatov, Head of Security Operations Center, Kaspersky.
For greater protection from advanced attacks, Kaspersky experts recommend the following:
- Deploy a solution that combines detection and response capabilities and help identify threats without involving additional in-house resources.
- Provide your SOC team with access to the latest threat intelligence and ensure in-depth visibility into cyberthreats targeting your organization.
- Provide your staff with essential cybersecurity knowledge to reduce the likelihood of targeted attacks.
- Implement expert Incident Response training to improve the expertise of your in-house digital forensics and incident response team.
The full Kaspersky Managed Detection and Response Analyst Report 2022 is available via this link.
About Kaspersky
Kaspersky is a global cybersecurity and digital privacy company founded in 1997. Kaspersky’s deep threat intelligence and security expertise is constantly transforming into innovative security solutions and services to protect businesses, critical infrastructure, governments and consumers around the globe. The company’s comprehensive security portfolio includes leading endpoint protection and a number of specialized security solutions and services to fight sophisticated and evolving digital threats. Over 400 million users are protected by Kaspersky technologies and we help 240,000 corporate clients protect what matters most to them. Learn more at www.kaspersky.com.
[1] The Managed Detection and Response Analyst Report 2022 presents the results of analysis of incidents detected by Kaspersky’s Security Operations Center (SOC) team. The report provides information about the most common attack tactics, techniques and tools, as well as the nature of detected incidents, their geography and distribution by sector. The results are achieved through the use of Kaspersky MDR.
[2] Kaspersky MDR is a 24/7 incident monitoring and response service powered by Kaspersky SOC technology and expertise.
[3] APT = Advanced persistent threat